diff --git a/.history b/.history
new file mode 100644
index 0000000000000000000000000000000000000000..90ad8d3759f01d46a7d76c9225eb6dc1b4a901ec
--- /dev/null
+++ b/.history
@@ -0,0 +1,113 @@
+commit 9450db11a189b4099ca8c5d4ccc4f303e2ee2320
+Author: Recolic <root@recolic.net>
+Date: Sun Jun 30 16:02:28 2019 +0800
+
+ Update README.md
+
+commit abbf82bfeba26c28a470447d3311236817e96d42
+Author: Recolic Keghart <root@recolic.net>
+Date: Tue Jun 11 21:33:38 2019 +0800
+
+ remove packed struct
+
+commit afed693fefd78a73dfd97e1b3929d619720b860a
+Author: Recolic Keghart <root@recolic.net>
+Date: Tue Jun 11 21:33:30 2019 +0800
+
+ remove packed struct
+
+commit 65ee23e090436f761ceb30fbff53638207d150de
+Author: Recolic Keghart <root@recolic.net>
+Date: Tue Jun 11 21:30:19 2019 +0800
+
+ update cmake
+
+commit 9f58b2ad47bddfdd338217f88a9491327a2d5f62
+Author: Recolic Keghart <root@recolic.net>
+Date: Tue Jun 11 21:27:26 2019 +0800
+
+ Done. Dynamic connection tested. (UDP lost control packet not tested!)
+
+commit 0badf744588c7e19b3ffbc02b9d384fb3ca8c669
+Author: Recolic Keghart <root@recolic.net>
+Date: Tue Jun 11 02:52:51 2019 +0800
+
+ DO NOT BUILD: finished but not debugged
+
+commit 13c1c79f50f28f365cc6938462047de9f9e37d3d
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 18:57:58 2019 +0800
+
+ update readme
+
+commit ae8ba24d6bdd5218bc3db1a9fe364b27b32b55ca
+Author: Recolic <root@recolic.net>
+Date: Mon Jun 10 18:52:33 2019 +0800
+
+ Create LICENSE
+
+commit 35225ec5403aa1a3b69b42c994c41954da096be6
+Author: Recolic <root@recolic.net>
+Date: Mon Jun 10 18:49:57 2019 +0800
+
+ Update README.md
+
+commit a51bf7957bdaaf8531c76f2750742eb40ba06002
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 18:49:00 2019 +0800
+
+ finished
+
+commit 3d48635f4dafba301574e8162296cb08dde36b0a
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 18:05:26 2019 +0800
+
+ bug fix
+
+commit 79da4564218eed98cecf2a9ec3866a7e0ca142e6
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 14:40:12 2019 +0800
+
+ bug fix
+
+commit 0675b0afedb596c141f49017ee7faf922419e068
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 13:26:20 2019 +0800
+
+ DO NOT BUILD: A failing version for TCP
+
+commit 58aa632ca4ddb281b92a3e1c311f7738471c805f
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 12:57:38 2019 +0800
+
+ seems working. push to server before cleanup
+
+commit ba09af0f49fcbb5abaa1b89cf7a536ae8cfc90e7
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 11:55:23 2019 +0800
+
+ bugfix
+
+commit a85df551ee45be323cad86109d41b022338b8b69
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 02:14:35 2019 +0800
+
+ bugfix
+
+commit 0c6943999f34bdf8f7fb6ae3b42c437b1c9aefac
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 01:56:48 2019 +0800
+
+ bugfix
+
+commit 956b8af2b912e6f3983a4c621ff74e27d2280a4b
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 01:52:24 2019 +0800
+
+ init
+
+commit 8cf5faddaa33926c98905dfd0184c2b39f61c5f6
+Author: Recolic Keghart <root@recolic.net>
+Date: Mon Jun 10 01:50:11 2019 +0800
+
+ init
diff --git a/CMakeLists.txt b/CMakeLists.txt
index b298babe029a8c0bdec4ecbf56e4a6e71938cc69..ab5a12d235533eecf070ae2c687fc541169823ad 100644
--- a/CMakeLists.txt
+++ b/CMakeLists.txt
@@ -1,14 +1,19 @@
-cmake_minimum_required(VERSION 3.14)
+cmake_minimum_required(VERSION 3.0)
project(udp_forwarder_ng)
find_package(rlib)
+find_package(Threads)
set(CMAKE_CXX_STANDARD 14)
+set(CMAKE_CXX_FLAGS_DEBUG "-g -DMALLOC_CHECK_=2")
+set(CMAKE_CXX_FLAGS_RELEASE "-O3")
include_directories(./lib)
include_directories(.)
-
-add_executable(udp_forwarder_ng main.cc Forwarder.hpp Crypto.hpp Dictionary.hpp)
+add_executable(udp_forwarder_ng main.cc Forwarder.hpp Crypto.hpp Config.hpp Util.hpp)
target_link_libraries(udp_forwarder_ng r)
-add_executable(crypto_test test/TestCrypto.cc Crypto.hpp Dictionary.hpp)
+target_link_libraries(udp_forwarder_ng Threads::Threads)
+add_executable(crypto_test test/TestCrypto.cc Crypto.hpp Config.hpp)
target_link_libraries(crypto_test r)
+
+install(TARGETS udp_forwarder_ng DESTINATION /usr/bin)
diff --git a/Dictionary.hpp b/Config.hpp
similarity index 96%
rename from Dictionary.hpp
rename to Config.hpp
index 3e2c5bb9211cdae568b38906e558a6cee9e9b917..543396dc228da8b1ec7f50fe9b9389db6c1d572a 100644
--- a/Dictionary.hpp
+++ b/Config.hpp
@@ -3,8 +3,19 @@
#include <string>
+// DGRAM packet usually smaller than 1400B.
+constexpr size_t DGRAM_BUFFER_SIZE = 20480; // 20KiB
+// epoll buffer size.
+constexpr size_t MAX_EVENTS = 16;
+
+// Change a connection on every n seconds,
+// to reset the GFW deep-packet-inspection process.
+// ( Only if server side is encrypted, so nothing happens
+// to the real openvpn server.
+constexpr size_t SERVER_ENCRYPT_CONNECTION_TIMEOUT_SECONDS = 60;
+
+// a random long string to fill the buffer.
const std::string crypto_dictionary = R"RSTR(
-
Optimizing C++/Code optimization/Faster operations
< Optimizing C++‎ | Code optimization
Jump to navigationJump to search
diff --git a/Crypto.hpp b/Crypto.hpp
index 6b34cf78cad326931a7c49142f98f642f307c529..28e3dae0636dce594a39aa2f60fdff2ed4d8e965 100644
--- a/Crypto.hpp
+++ b/Crypto.hpp
@@ -8,7 +8,7 @@
#include <string>
#include <numeric>
#include <limits>
-#include "Dictionary.hpp"
+#include "Config.hpp"
#if defined(__linux__)
# include <endian.h>
@@ -25,10 +25,12 @@
using std::string;
+// WARNING: should be thread-safe.
class Crypto {
public:
Crypto() = default;
void convertL2R(string &data, const string &lKey, const string &rKey) {
+ // If data is empty, maybe it's a bare control msg: a exception maybe thrown.
// If lKey is not null, decrypt the data.
// If rKey is not null, encrypt the data.
if(!lKey.empty()) {
@@ -85,6 +87,8 @@ private:
if(data.size() < 8)
throw std::runtime_error("Decrypt: Data length less than 8. ");
string nonce = data.substr(0, 8);
+ if(uint64FromBinStr(nonce) == 0)
+ throw std::runtime_error("Bad nonce: nonce is zero: ctl msg not fucked.");
string toDecrypt = data.substr(8);
block_decrypt(toDecrypt, key, nonce);
@@ -106,6 +110,7 @@ private:
size_t dict_current_index = 0;
struct {
+ // This rand is just QUICK and good enough. Maybe still good enough for multi-threading.
uint64_t x=123456789, y=362436069, z=521288629;
uint64_t get() {
uint64_t t;
@@ -118,7 +123,10 @@ private:
y = z;
z = t ^ x ^ y;
- return z;
+ if(z != 0) // nonce can not be zero. zero nonce means control message.
+ return z;
+ else
+ return get();
}
} xorshf_rand;
diff --git a/Forwarder.hpp b/Forwarder.hpp
index d6f2f9b29dcf7d89a6b16d344c9539348ffb076b..c106628b8987ec68a96dc60ba1e7cd268aa1ddad 100644
--- a/Forwarder.hpp
+++ b/Forwarder.hpp
@@ -9,12 +9,38 @@
#include <picosha2.h>
#include <rlib/sys/sio.hpp>
#include <sys/epoll.h>
-#include <rlib/stdio.hpp>
-#include "Crypto.hpp"
+#include <thread>
+#include <Crypto.hpp>
+#include <unordered_map>
+#include "Config.hpp"
+#include "Util.hpp"
using std::string;
using namespace std::literals;
+inline void epoll_add_fd(fd_t epollFd, fd_t fd) {
+ epoll_event event {
+ .events = EPOLLIN,
+ .data = {
+ .fd = fd,
+ }
+ };
+ auto ret1 = epoll_ctl(epollFd, EPOLL_CTL_ADD, fd, &event);
+ if(ret1 == -1)
+ throw std::runtime_error("epoll_ctl failed.");
+}
+inline void epoll_del_fd(fd_t epollFd, fd_t fd) {
+ epoll_event event {
+ .events = EPOLLIN,
+ .data = {
+ .fd = fd,
+ }
+ };
+ auto ret1 = epoll_ctl(epollFd, EPOLL_CTL_DEL, fd, &event); // Can be nullptr since linux 2.6.9
+ if(ret1 == -1)
+ throw std::runtime_error("epoll_ctl failed.");
+}
+
class Forwarder {
public:
Forwarder(string listenAddr, uint16_t listenPort, string serverAddr, uint16_t serverPort, string lPassword,
@@ -29,40 +55,50 @@ public:
rKey = "";
}
-private:
- auto setup_epoll(fd_t listenFd, fd_t serverFd) {
- auto epollFd = epoll_create1(NULL);
- if(epollFd == -1)
- throw std::runtime_error("Failed to create epoll fd.");
-
- // setup epoll.
- epoll_event eventL {
- .events = EPOLLIN,
- .data.fd = listenFd,
- }, eventS {
- .events = EPOLLIN,
- .data.fd = serverFd,
- };
- auto ret1 = epoll_ctl(epollFd, EPOLL_CTL_ADD, listenFd, &eventL);
- auto ret2 = epoll_ctl(epollFd, EPOLL_CTL_ADD, serverFd, &eventS);
- if(ret1 == -1 or ret2 == -1)
- throw std::runtime_error("epoll_ctl failed.");
- return epollFd;
- }
-
public:
[[noreturn]] void run() {
- // setup connections.
auto listenFd = rlib::quick_listen(listenAddr, listenPort, true);
- auto serverFd = rlib::quick_connect(serverAddr, serverPort, true);
- auto epollFd = setup_epoll(listenFd, serverFd);
+ rlib_defer([=]{close(listenFd);});
+
+ auto epollFd = epoll_create1(0);
+ if(epollFd == -1)
+ throw std::runtime_error("Failed to create epoll fd.");
+ epoll_add_fd(epollFd, listenFd);
- constexpr size_t MAX_EVENTS = 16;
epoll_event events[MAX_EVENTS];
- // DGRAM packet usually smaller than 1400B.
- constexpr size_t DGRAM_BUFFER_SIZE = 20480; // 20KiB
char buffer[DGRAM_BUFFER_SIZE];
+ // WARN: If you want to modify this program to work for both TCP and UDP, PLEASE use rlib::sockIO::recv instead of fixed buffer.
+
+ // Map from serverSession to clientSession.
+ // If I see a packet from client, throw it to server.
+ // If I see a packet from server, I have to determine which client to throw it.
+ // So I have to record the map between client and server, one-to-one.
+
+ std::unordered_map<clientInfo, fd_t, clientInfoHash> client2server;
+ std::unordered_map<fd_t, clientInfo> server2client;
+ std::unordered_map<fd_t, size_t> server2wallTime;
+ // If connection creation time is less than walltime, the connection timed out.
+
+ auto connForNewClient = [&, this](const clientInfo &info) {
+ if(info.isNull()) throw std::runtime_error("Invalid client info");
+ auto serverFd = rlib::quick_connect(serverAddr, serverPort, true);
+ rlog.verbose("creating new connection... {}", serverFd);
+ client2server[info] = serverFd; // May overwrite existing element on server timing out.
+ server2client.insert(std::make_pair(serverFd, info));
+ server2wallTime.insert(std::make_pair(serverFd, getWallTime()));
+ epoll_add_fd(epollFd, serverFd);
+ return serverFd;
+ };
+ auto eraseServerConn = [&](fd_t fd) {
+ server2client.erase(fd);
+ server2wallTime.erase(fd);
+ epoll_del_fd(epollFd, fd);
+ close(fd);
+ };
+
+ rlog.info("Forwarding server working...");
+ rlog.info("Listening {}:{}, with upstream server {}:{}.", listenAddr, listenPort, serverAddr, serverPort);
// Main loop!
while(true) {
@@ -71,31 +107,169 @@ public:
throw std::runtime_error("epoll_wait failed.");
for(auto cter = 0; cter < nfds; ++cter) {
- auto recvFd = events[cter].data.fd;
- auto recvSideIsListenSide = recvFd == listenFd;
- auto anotherFd = recvSideIsListenSide ? serverFd : listenFd;
- const auto &recvSideKey = recvSideIsListenSide ? lKey : rKey;
- const auto &sendSideKey = recvSideIsListenSide ? rKey : lKey;
+ const auto recvFd = events[cter].data.fd;
+ const auto recvSideIsClientSide = server2client.find(recvFd) == server2client.end(); // is not server
+ const auto &recvSideKey = recvSideIsClientSide ? lKey : rKey;
+ const auto &sendSideKey = recvSideIsClientSide ? rKey : lKey;
+ rlog.debug("woke up fd {}, isCLient={}", recvFd, recvSideIsClientSide);
try {
- auto size = recvfrom(recvFd, buffer, DGRAM_BUFFER_SIZE, NULL, NULL, NULL);
- if(size == -1) {
- throw std::runtime_error("ERR: recvfrom returns -1. "s + strerror(errno));
+ size_t size;
+ fd_t anotherFd;
+ sockaddr *sendtoAddr = nullptr;
+ socklen_t sendtoAddrLen = 0;
+ clientInfo clientSideInfo;
+ // Recv /////////////////////////////////////////////////////////////////////////////////////
+ if(recvSideIsClientSide) {
+ // Client to Server packet.
+ auto &info = clientSideInfo;
+ size = recvfrom(recvFd, buffer, DGRAM_BUFFER_SIZE, 0, (sockaddr *)&info.addr, &info.len);
+ if(size == -1)
+ throw std::runtime_error("ERR: recvfrom returns -1. "s + strerror(errno));
+ auto pos = client2server.find(info);
+ if(pos == client2server.end())
+ anotherFd = connForNewClient(info);
+ else
+ anotherFd = pos->second;
+ }
+ else {
+ // Server to Client packet.
+ size = recvfrom(recvFd, buffer, DGRAM_BUFFER_SIZE, 0, nullptr, nullptr);
+ if(size == -1)
+ throw std::runtime_error("ERR: recvfrom returns -1. "s + strerror(errno));
+ clientInfo &info = server2client.at(recvFd); // If server not found, drop the msg. (The server may just timed out)
+ sendtoAddr = (sockaddr *)&info.addr;
+ sendtoAddrLen = info.len;
+ anotherFd = listenFd;
+ clientSideInfo = info;
}
+ // received raw data.
string bufferStr (std::begin(buffer), std::begin(buffer) + size);
+
+ // Addon: ConnTimeout ///////////////////////////////////////////////////////////////////////////
+ // Recolic: The GFW use deep-packet-inspection to fuck my OpenVPN connection in about 10 minutes.
+ // What if I change a new connection in every 1 minute?
+ // Try it.
+
+ if(bufferStr.size() >= sizeof(uint64_t)) {
+ // Check control msg. Its nonce is zero.
+ if(*(uint64_t*)bufferStr.data() == 0) {
+ if(recvSideIsClientSide) {
+ // ctl msg from client. (conn change req)
+ uint16_t previous_port, new_port;
+ if(bufferStr.size() < sizeof(uint64_t) + 2*sizeof(previous_port))
+ throw std::runtime_error("ctl msg from client too short.");
+ std::memcpy(&previous_port, bufferStr.data()+sizeof(uint64_t), sizeof(previous_port));
+ std::memcpy(&new_port, bufferStr.data()+sizeof(uint64_t)+sizeof(previous_port), sizeof(previous_port));
+ previous_port = be16toh(previous_port);
+ new_port = be16toh(new_port);
+
+ // getsockname on UDP ONLY works for the local port. Ignore the addr!
+ auto iter = std::find_if(client2server.begin(), client2server.end(), [previous_port](const auto &kv){
+ // Known bug 1632: If there's two udp client with different addr and same port. it booms.
+ return kv.first.getPortNum() == previous_port;
+ });
+ if(iter == client2server.end())
+ throw std::runtime_error("ctl msg from client: change conn: prev conn not exist.");
+
+ auto clientSideInfoBackup = clientSideInfo;
+ clientSideInfo.setPortNum(new_port);
+ auto serverFd = iter->second;
+ rlog.debug("Client requested to change conn:", previous_port, new_port);
+ server2client[serverFd].setPortNum(new_port);
+ client2server[clientSideInfo] = serverFd; // Old record is not erased now.
+
+ // send ACK to client(recvFd). Should use previous port.
+ // The client will see the ACK from OLD connection and erase it.
+ string ackStr (sizeof(uint64_t), '\0');
+ auto ret = sendto(recvFd, ackStr.data(), ackStr.size(), 0, (sockaddr*)&clientSideInfoBackup.addr, clientSideInfoBackup.len);
+ if(ret == -1)
+ throw std::runtime_error("Failed to send CONN CHANGE ACK");
+
+ // remove the ctl prefix
+ bufferStr = bufferStr.substr(sizeof(uint64_t) + 2*sizeof(previous_port));
+ }
+ else {
+ // ACK ctl msg from server (conn change ack)
+ if(bufferStr.size() != sizeof(uint64_t))
+ throw std::runtime_error("wrong ack ctl from server");
+ rlog.verbose("REMOVEING FD", recvFd);
+ eraseServerConn(recvFd);
+ continue; // nothing todo with bare ACK.
+ }
+ }
+ }
+
+ // Encrypt/Decrypt ///////////////////////////////////////////////////////////////////////////////
crypto.convertL2R(bufferStr, recvSideKey, sendSideKey);
+ // Encrypt/Decrypt End. Continue ConnTimeout Addon ///////////////////////////////////////////////
+
+ auto prepareConnChangeReq = [&](fd_t prevFd, fd_t newFd) {
+ clientInfo previous, newOne;
+ newOne.len = previous.len = sizeof(previous.addr);
+ auto ret = getsockname(prevFd, (sockaddr*)&previous.addr, &previous.len) +
+ getsockname(newFd, (sockaddr*)&newOne.addr, &newOne.len);
+ if(ret != 0)
+ throw std::runtime_error("getsockname failed.");
+ auto previous_port = htobe16(previous.getPortNum()),
+ new_port = htobe16(newOne.getPortNum());
+ rlog.debug("COnnChangeReq (port num in BIG ENDIAN):", previous_port, new_port);
+
+ // Add control header.
+ bufferStr = string(sizeof(uint64_t) + sizeof(previous_port)*2, '\0') + bufferStr;
+ std::memcpy((char*)bufferStr.data()+sizeof(uint64_t), &previous_port, sizeof(previous_port));
+ std::memcpy((char*)bufferStr.data()+sizeof(uint64_t)+sizeof(previous_port), &new_port, sizeof(new_port));
+ };
+
+ if(recvSideIsClientSide && !sendSideKey.empty()) {
+ // Check server connection timeout.
+ // Only timeout the connection if server-side is encrypted. Or OpenVPN server will confuse.
+ // If the connection is timeout:
+ // 1. Create the new connection, reset timeout, update client2server and insert server2client.
+ // 2. Attach the control header onto the origin data packet, send it on the new connection.
+ // When received message from server, if server2client doesn't match client2server, meaning
+ // that this connection is already timed out.
+ // If the message is ACK control message, remove the old entry in server2client.
+ // Otherwise, resend the bare control header in previous step 2.
+ if(server2wallTime.at(anotherFd) < getWallTime()) {
+ // This connection timed out.
+ rlog.verbose("A Connection timed out, creating new conn...");
+ auto newConnFd = connForNewClient(clientSideInfo);
+ prepareConnChangeReq(anotherFd, newConnFd);
+ }
+ }
- size = sendto(anotherFd, bufferStr.data(), bufferStr.size(), NULL, NULL, NULL);
+ if(!recvSideIsClientSide) {
+ // server to client: I said to change conn but server still using old conn.
+ // Maybe my req lost. resend.
+ auto clientOwnerFd = client2server.at(server2client.at(recvFd));
+ if(clientOwnerFd != recvFd) {
+ // Client2server already modified, but not receiving ACK.
+ prepareConnChangeReq(recvFd, clientOwnerFd);
+ }
+ }
+
+ // Send /////////////////////////////////////////////////////////////////////////////////////
+ rlog.debug("sending on fd", anotherFd);
+ if(recvSideIsClientSide) {
+ // Client to Server packet.
+ size = send(anotherFd, bufferStr.data(), bufferStr.size(), 0);
+ }
+ else {
+ // Server to Client packet.
+ size = sendto(anotherFd, bufferStr.data(), bufferStr.size(), 0, sendtoAddr, sendtoAddrLen);
+ }
if(size == -1) {
- throw std::runtime_error("ERR: sendto returns -1. "s + strerror(errno));
+ throw std::runtime_error("sendto returns -1. "s + strerror(errno));
}
if(size != bufferStr.size()) {
- rlib::println("ERR: sendto not sent all data.");
+ rlog.warning("sendto not sent all data.");
}
+ // Done /////////////////////////////////////////////////////////////////////////////////////
}
catch(std::exception &e) {
- rlib::println(e.what());
+ rlog.error(e.what());
}
}
}
diff --git a/LICENSE b/LICENSE
new file mode 100644
index 0000000000000000000000000000000000000000..f288702d2fa16d3cdf0035b15a9fcbc552cd88e7
--- /dev/null
+++ b/LICENSE
@@ -0,0 +1,674 @@
+ GNU GENERAL PUBLIC LICENSE
+ Version 3, 29 June 2007
+
+ Copyright (C) 2007 Free Software Foundation, Inc. <https://fsf.org/>
+ Everyone is permitted to copy and distribute verbatim copies
+ of this license document, but changing it is not allowed.
+
+ Preamble
+
+ The GNU General Public License is a free, copyleft license for
+software and other kinds of works.
+
+ The licenses for most software and other practical works are designed
+to take away your freedom to share and change the works. By contrast,
+the GNU General Public License is intended to guarantee your freedom to
+share and change all versions of a program--to make sure it remains free
+software for all its users. We, the Free Software Foundation, use the
+GNU General Public License for most of our software; it applies also to
+any other work released this way by its authors. You can apply it to
+your programs, too.
+
+ When we speak of free software, we are referring to freedom, not
+price. Our General Public Licenses are designed to make sure that you
+have the freedom to distribute copies of free software (and charge for
+them if you wish), that you receive source code or can get it if you
+want it, that you can change the software or use pieces of it in new
+free programs, and that you know you can do these things.
+
+ To protect your rights, we need to prevent others from denying you
+these rights or asking you to surrender the rights. Therefore, you have
+certain responsibilities if you distribute copies of the software, or if
+you modify it: responsibilities to respect the freedom of others.
+
+ For example, if you distribute copies of such a program, whether
+gratis or for a fee, you must pass on to the recipients the same
+freedoms that you received. You must make sure that they, too, receive
+or can get the source code. And you must show them these terms so they
+know their rights.
+
+ Developers that use the GNU GPL protect your rights with two steps:
+(1) assert copyright on the software, and (2) offer you this License
+giving you legal permission to copy, distribute and/or modify it.
+
+ For the developers' and authors' protection, the GPL clearly explains
+that there is no warranty for this free software. For both users' and
+authors' sake, the GPL requires that modified versions be marked as
+changed, so that their problems will not be attributed erroneously to
+authors of previous versions.
+
+ Some devices are designed to deny users access to install or run
+modified versions of the software inside them, although the manufacturer
+can do so. This is fundamentally incompatible with the aim of
+protecting users' freedom to change the software. The systematic
+pattern of such abuse occurs in the area of products for individuals to
+use, which is precisely where it is most unacceptable. Therefore, we
+have designed this version of the GPL to prohibit the practice for those
+products. If such problems arise substantially in other domains, we
+stand ready to extend this provision to those domains in future versions
+of the GPL, as needed to protect the freedom of users.
+
+ Finally, every program is threatened constantly by software patents.
+States should not allow patents to restrict development and use of
+software on general-purpose computers, but in those that do, we wish to
+avoid the special danger that patents applied to a free program could
+make it effectively proprietary. To prevent this, the GPL assures that
+patents cannot be used to render the program non-free.
+
+ The precise terms and conditions for copying, distribution and
+modification follow.
+
+ TERMS AND CONDITIONS
+
+ 0. Definitions.
+
+ "This License" refers to version 3 of the GNU General Public License.
+
+ "Copyright" also means copyright-like laws that apply to other kinds of
+works, such as semiconductor masks.
+
+ "The Program" refers to any copyrightable work licensed under this
+License. Each licensee is addressed as "you". "Licensees" and
+"recipients" may be individuals or organizations.
+
+ To "modify" a work means to copy from or adapt all or part of the work
+in a fashion requiring copyright permission, other than the making of an
+exact copy. The resulting work is called a "modified version" of the
+earlier work or a work "based on" the earlier work.
+
+ A "covered work" means either the unmodified Program or a work based
+on the Program.
+
+ To "propagate" a work means to do anything with it that, without
+permission, would make you directly or secondarily liable for
+infringement under applicable copyright law, except executing it on a
+computer or modifying a private copy. Propagation includes copying,
+distribution (with or without modification), making available to the
+public, and in some countries other activities as well.
+
+ To "convey" a work means any kind of propagation that enables other
+parties to make or receive copies. Mere interaction with a user through
+a computer network, with no transfer of a copy, is not conveying.
+
+ An interactive user interface displays "Appropriate Legal Notices"
+to the extent that it includes a convenient and prominently visible
+feature that (1) displays an appropriate copyright notice, and (2)
+tells the user that there is no warranty for the work (except to the
+extent that warranties are provided), that licensees may convey the
+work under this License, and how to view a copy of this License. If
+the interface presents a list of user commands or options, such as a
+menu, a prominent item in the list meets this criterion.
+
+ 1. Source Code.
+
+ The "source code" for a work means the preferred form of the work
+for making modifications to it. "Object code" means any non-source
+form of a work.
+
+ A "Standard Interface" means an interface that either is an official
+standard defined by a recognized standards body, or, in the case of
+interfaces specified for a particular programming language, one that
+is widely used among developers working in that language.
+
+ The "System Libraries" of an executable work include anything, other
+than the work as a whole, that (a) is included in the normal form of
+packaging a Major Component, but which is not part of that Major
+Component, and (b) serves only to enable use of the work with that
+Major Component, or to implement a Standard Interface for which an
+implementation is available to the public in source code form. A
+"Major Component", in this context, means a major essential component
+(kernel, window system, and so on) of the specific operating system
+(if any) on which the executable work runs, or a compiler used to
+produce the work, or an object code interpreter used to run it.
+
+ The "Corresponding Source" for a work in object code form means all
+the source code needed to generate, install, and (for an executable
+work) run the object code and to modify the work, including scripts to
+control those activities. However, it does not include the work's
+System Libraries, or general-purpose tools or generally available free
+programs which are used unmodified in performing those activities but
+which are not part of the work. For example, Corresponding Source
+includes interface definition files associated with source files for
+the work, and the source code for shared libraries and dynamically
+linked subprograms that the work is specifically designed to require,
+such as by intimate data communication or control flow between those
+subprograms and other parts of the work.
+
+ The Corresponding Source need not include anything that users
+can regenerate automatically from other parts of the Corresponding
+Source.
+
+ The Corresponding Source for a work in source code form is that
+same work.
+
+ 2. Basic Permissions.
+
+ All rights granted under this License are granted for the term of
+copyright on the Program, and are irrevocable provided the stated
+conditions are met. This License explicitly affirms your unlimited
+permission to run the unmodified Program. The output from running a
+covered work is covered by this License only if the output, given its
+content, constitutes a covered work. This License acknowledges your
+rights of fair use or other equivalent, as provided by copyright law.
+
+ You may make, run and propagate covered works that you do not
+convey, without conditions so long as your license otherwise remains
+in force. You may convey covered works to others for the sole purpose
+of having them make modifications exclusively for you, or provide you
+with facilities for running those works, provided that you comply with
+the terms of this License in conveying all material for which you do
+not control copyright. Those thus making or running the covered works
+for you must do so exclusively on your behalf, under your direction
+and control, on terms that prohibit them from making any copies of
+your copyrighted material outside their relationship with you.
+
+ Conveying under any other circumstances is permitted solely under
+the conditions stated below. Sublicensing is not allowed; section 10
+makes it unnecessary.
+
+ 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
+
+ No covered work shall be deemed part of an effective technological
+measure under any applicable law fulfilling obligations under article
+11 of the WIPO copyright treaty adopted on 20 December 1996, or
+similar laws prohibiting or restricting circumvention of such
+measures.
+
+ When you convey a covered work, you waive any legal power to forbid
+circumvention of technological measures to the extent such circumvention
+is effected by exercising rights under this License with respect to
+the covered work, and you disclaim any intention to limit operation or
+modification of the work as a means of enforcing, against the work's
+users, your or third parties' legal rights to forbid circumvention of
+technological measures.
+
+ 4. Conveying Verbatim Copies.
+
+ You may convey verbatim copies of the Program's source code as you
+receive it, in any medium, provided that you conspicuously and
+appropriately publish on each copy an appropriate copyright notice;
+keep intact all notices stating that this License and any
+non-permissive terms added in accord with section 7 apply to the code;
+keep intact all notices of the absence of any warranty; and give all
+recipients a copy of this License along with the Program.
+
+ You may charge any price or no price for each copy that you convey,
+and you may offer support or warranty protection for a fee.
+
+ 5. Conveying Modified Source Versions.
+
+ You may convey a work based on the Program, or the modifications to
+produce it from the Program, in the form of source code under the
+terms of section 4, provided that you also meet all of these conditions:
+
+ a) The work must carry prominent notices stating that you modified
+ it, and giving a relevant date.
+
+ b) The work must carry prominent notices stating that it is
+ released under this License and any conditions added under section
+ 7. This requirement modifies the requirement in section 4 to
+ "keep intact all notices".
+
+ c) You must license the entire work, as a whole, under this
+ License to anyone who comes into possession of a copy. This
+ License will therefore apply, along with any applicable section 7
+ additional terms, to the whole of the work, and all its parts,
+ regardless of how they are packaged. This License gives no
+ permission to license the work in any other way, but it does not
+ invalidate such permission if you have separately received it.
+
+ d) If the work has interactive user interfaces, each must display
+ Appropriate Legal Notices; however, if the Program has interactive
+ interfaces that do not display Appropriate Legal Notices, your
+ work need not make them do so.
+
+ A compilation of a covered work with other separate and independent
+works, which are not by their nature extensions of the covered work,
+and which are not combined with it such as to form a larger program,
+in or on a volume of a storage or distribution medium, is called an
+"aggregate" if the compilation and its resulting copyright are not
+used to limit the access or legal rights of the compilation's users
+beyond what the individual works permit. Inclusion of a covered work
+in an aggregate does not cause this License to apply to the other
+parts of the aggregate.
+
+ 6. Conveying Non-Source Forms.
+
+ You may convey a covered work in object code form under the terms
+of sections 4 and 5, provided that you also convey the
+machine-readable Corresponding Source under the terms of this License,
+in one of these ways:
+
+ a) Convey the object code in, or embodied in, a physical product
+ (including a physical distribution medium), accompanied by the
+ Corresponding Source fixed on a durable physical medium
+ customarily used for software interchange.
+
+ b) Convey the object code in, or embodied in, a physical product
+ (including a physical distribution medium), accompanied by a
+ written offer, valid for at least three years and valid for as
+ long as you offer spare parts or customer support for that product
+ model, to give anyone who possesses the object code either (1) a
+ copy of the Corresponding Source for all the software in the
+ product that is covered by this License, on a durable physical
+ medium customarily used for software interchange, for a price no
+ more than your reasonable cost of physically performing this
+ conveying of source, or (2) access to copy the
+ Corresponding Source from a network server at no charge.
+
+ c) Convey individual copies of the object code with a copy of the
+ written offer to provide the Corresponding Source. This
+ alternative is allowed only occasionally and noncommercially, and
+ only if you received the object code with such an offer, in accord
+ with subsection 6b.
+
+ d) Convey the object code by offering access from a designated
+ place (gratis or for a charge), and offer equivalent access to the
+ Corresponding Source in the same way through the same place at no
+ further charge. You need not require recipients to copy the
+ Corresponding Source along with the object code. If the place to
+ copy the object code is a network server, the Corresponding Source
+ may be on a different server (operated by you or a third party)
+ that supports equivalent copying facilities, provided you maintain
+ clear directions next to the object code saying where to find the
+ Corresponding Source. Regardless of what server hosts the
+ Corresponding Source, you remain obligated to ensure that it is
+ available for as long as needed to satisfy these requirements.
+
+ e) Convey the object code using peer-to-peer transmission, provided
+ you inform other peers where the object code and Corresponding
+ Source of the work are being offered to the general public at no
+ charge under subsection 6d.
+
+ A separable portion of the object code, whose source code is excluded
+from the Corresponding Source as a System Library, need not be
+included in conveying the object code work.
+
+ A "User Product" is either (1) a "consumer product", which means any
+tangible personal property which is normally used for personal, family,
+or household purposes, or (2) anything designed or sold for incorporation
+into a dwelling. In determining whether a product is a consumer product,
+doubtful cases shall be resolved in favor of coverage. For a particular
+product received by a particular user, "normally used" refers to a
+typical or common use of that class of product, regardless of the status
+of the particular user or of the way in which the particular user
+actually uses, or expects or is expected to use, the product. A product
+is a consumer product regardless of whether the product has substantial
+commercial, industrial or non-consumer uses, unless such uses represent
+the only significant mode of use of the product.
+
+ "Installation Information" for a User Product means any methods,
+procedures, authorization keys, or other information required to install
+and execute modified versions of a covered work in that User Product from
+a modified version of its Corresponding Source. The information must
+suffice to ensure that the continued functioning of the modified object
+code is in no case prevented or interfered with solely because
+modification has been made.
+
+ If you convey an object code work under this section in, or with, or
+specifically for use in, a User Product, and the conveying occurs as
+part of a transaction in which the right of possession and use of the
+User Product is transferred to the recipient in perpetuity or for a
+fixed term (regardless of how the transaction is characterized), the
+Corresponding Source conveyed under this section must be accompanied
+by the Installation Information. But this requirement does not apply
+if neither you nor any third party retains the ability to install
+modified object code on the User Product (for example, the work has
+been installed in ROM).
+
+ The requirement to provide Installation Information does not include a
+requirement to continue to provide support service, warranty, or updates
+for a work that has been modified or installed by the recipient, or for
+the User Product in which it has been modified or installed. Access to a
+network may be denied when the modification itself materially and
+adversely affects the operation of the network or violates the rules and
+protocols for communication across the network.
+
+ Corresponding Source conveyed, and Installation Information provided,
+in accord with this section must be in a format that is publicly
+documented (and with an implementation available to the public in
+source code form), and must require no special password or key for
+unpacking, reading or copying.
+
+ 7. Additional Terms.
+
+ "Additional permissions" are terms that supplement the terms of this
+License by making exceptions from one or more of its conditions.
+Additional permissions that are applicable to the entire Program shall
+be treated as though they were included in this License, to the extent
+that they are valid under applicable law. If additional permissions
+apply only to part of the Program, that part may be used separately
+under those permissions, but the entire Program remains governed by
+this License without regard to the additional permissions.
+
+ When you convey a copy of a covered work, you may at your option
+remove any additional permissions from that copy, or from any part of
+it. (Additional permissions may be written to require their own
+removal in certain cases when you modify the work.) You may place
+additional permissions on material, added by you to a covered work,
+for which you have or can give appropriate copyright permission.
+
+ Notwithstanding any other provision of this License, for material you
+add to a covered work, you may (if authorized by the copyright holders of
+that material) supplement the terms of this License with terms:
+
+ a) Disclaiming warranty or limiting liability differently from the
+ terms of sections 15 and 16 of this License; or
+
+ b) Requiring preservation of specified reasonable legal notices or
+ author attributions in that material or in the Appropriate Legal
+ Notices displayed by works containing it; or
+
+ c) Prohibiting misrepresentation of the origin of that material, or
+ requiring that modified versions of such material be marked in
+ reasonable ways as different from the original version; or
+
+ d) Limiting the use for publicity purposes of names of licensors or
+ authors of the material; or
+
+ e) Declining to grant rights under trademark law for use of some
+ trade names, trademarks, or service marks; or
+
+ f) Requiring indemnification of licensors and authors of that
+ material by anyone who conveys the material (or modified versions of
+ it) with contractual assumptions of liability to the recipient, for
+ any liability that these contractual assumptions directly impose on
+ those licensors and authors.
+
+ All other non-permissive additional terms are considered "further
+restrictions" within the meaning of section 10. If the Program as you
+received it, or any part of it, contains a notice stating that it is
+governed by this License along with a term that is a further
+restriction, you may remove that term. If a license document contains
+a further restriction but permits relicensing or conveying under this
+License, you may add to a covered work material governed by the terms
+of that license document, provided that the further restriction does
+not survive such relicensing or conveying.
+
+ If you add terms to a covered work in accord with this section, you
+must place, in the relevant source files, a statement of the
+additional terms that apply to those files, or a notice indicating
+where to find the applicable terms.
+
+ Additional terms, permissive or non-permissive, may be stated in the
+form of a separately written license, or stated as exceptions;
+the above requirements apply either way.
+
+ 8. Termination.
+
+ You may not propagate or modify a covered work except as expressly
+provided under this License. Any attempt otherwise to propagate or
+modify it is void, and will automatically terminate your rights under
+this License (including any patent licenses granted under the third
+paragraph of section 11).
+
+ However, if you cease all violation of this License, then your
+license from a particular copyright holder is reinstated (a)
+provisionally, unless and until the copyright holder explicitly and
+finally terminates your license, and (b) permanently, if the copyright
+holder fails to notify you of the violation by some reasonable means
+prior to 60 days after the cessation.
+
+ Moreover, your license from a particular copyright holder is
+reinstated permanently if the copyright holder notifies you of the
+violation by some reasonable means, this is the first time you have
+received notice of violation of this License (for any work) from that
+copyright holder, and you cure the violation prior to 30 days after
+your receipt of the notice.
+
+ Termination of your rights under this section does not terminate the
+licenses of parties who have received copies or rights from you under
+this License. If your rights have been terminated and not permanently
+reinstated, you do not qualify to receive new licenses for the same
+material under section 10.
+
+ 9. Acceptance Not Required for Having Copies.
+
+ You are not required to accept this License in order to receive or
+run a copy of the Program. Ancillary propagation of a covered work
+occurring solely as a consequence of using peer-to-peer transmission
+to receive a copy likewise does not require acceptance. However,
+nothing other than this License grants you permission to propagate or
+modify any covered work. These actions infringe copyright if you do
+not accept this License. Therefore, by modifying or propagating a
+covered work, you indicate your acceptance of this License to do so.
+
+ 10. Automatic Licensing of Downstream Recipients.
+
+ Each time you convey a covered work, the recipient automatically
+receives a license from the original licensors, to run, modify and
+propagate that work, subject to this License. You are not responsible
+for enforcing compliance by third parties with this License.
+
+ An "entity transaction" is a transaction transferring control of an
+organization, or substantially all assets of one, or subdividing an
+organization, or merging organizations. If propagation of a covered
+work results from an entity transaction, each party to that
+transaction who receives a copy of the work also receives whatever
+licenses to the work the party's predecessor in interest had or could
+give under the previous paragraph, plus a right to possession of the
+Corresponding Source of the work from the predecessor in interest, if
+the predecessor has it or can get it with reasonable efforts.
+
+ You may not impose any further restrictions on the exercise of the
+rights granted or affirmed under this License. For example, you may
+not impose a license fee, royalty, or other charge for exercise of
+rights granted under this License, and you may not initiate litigation
+(including a cross-claim or counterclaim in a lawsuit) alleging that
+any patent claim is infringed by making, using, selling, offering for
+sale, or importing the Program or any portion of it.
+
+ 11. Patents.
+
+ A "contributor" is a copyright holder who authorizes use under this
+License of the Program or a work on which the Program is based. The
+work thus licensed is called the contributor's "contributor version".
+
+ A contributor's "essential patent claims" are all patent claims
+owned or controlled by the contributor, whether already acquired or
+hereafter acquired, that would be infringed by some manner, permitted
+by this License, of making, using, or selling its contributor version,
+but do not include claims that would be infringed only as a
+consequence of further modification of the contributor version. For
+purposes of this definition, "control" includes the right to grant
+patent sublicenses in a manner consistent with the requirements of
+this License.
+
+ Each contributor grants you a non-exclusive, worldwide, royalty-free
+patent license under the contributor's essential patent claims, to
+make, use, sell, offer for sale, import and otherwise run, modify and
+propagate the contents of its contributor version.
+
+ In the following three paragraphs, a "patent license" is any express
+agreement or commitment, however denominated, not to enforce a patent
+(such as an express permission to practice a patent or covenant not to
+sue for patent infringement). To "grant" such a patent license to a
+party means to make such an agreement or commitment not to enforce a
+patent against the party.
+
+ If you convey a covered work, knowingly relying on a patent license,
+and the Corresponding Source of the work is not available for anyone
+to copy, free of charge and under the terms of this License, through a
+publicly available network server or other readily accessible means,
+then you must either (1) cause the Corresponding Source to be so
+available, or (2) arrange to deprive yourself of the benefit of the
+patent license for this particular work, or (3) arrange, in a manner
+consistent with the requirements of this License, to extend the patent
+license to downstream recipients. "Knowingly relying" means you have
+actual knowledge that, but for the patent license, your conveying the
+covered work in a country, or your recipient's use of the covered work
+in a country, would infringe one or more identifiable patents in that
+country that you have reason to believe are valid.
+
+ If, pursuant to or in connection with a single transaction or
+arrangement, you convey, or propagate by procuring conveyance of, a
+covered work, and grant a patent license to some of the parties
+receiving the covered work authorizing them to use, propagate, modify
+or convey a specific copy of the covered work, then the patent license
+you grant is automatically extended to all recipients of the covered
+work and works based on it.
+
+ A patent license is "discriminatory" if it does not include within
+the scope of its coverage, prohibits the exercise of, or is
+conditioned on the non-exercise of one or more of the rights that are
+specifically granted under this License. You may not convey a covered
+work if you are a party to an arrangement with a third party that is
+in the business of distributing software, under which you make payment
+to the third party based on the extent of your activity of conveying
+the work, and under which the third party grants, to any of the
+parties who would receive the covered work from you, a discriminatory
+patent license (a) in connection with copies of the covered work
+conveyed by you (or copies made from those copies), or (b) primarily
+for and in connection with specific products or compilations that
+contain the covered work, unless you entered into that arrangement,
+or that patent license was granted, prior to 28 March 2007.
+
+ Nothing in this License shall be construed as excluding or limiting
+any implied license or other defenses to infringement that may
+otherwise be available to you under applicable patent law.
+
+ 12. No Surrender of Others' Freedom.
+
+ If conditions are imposed on you (whether by court order, agreement or
+otherwise) that contradict the conditions of this License, they do not
+excuse you from the conditions of this License. If you cannot convey a
+covered work so as to satisfy simultaneously your obligations under this
+License and any other pertinent obligations, then as a consequence you may
+not convey it at all. For example, if you agree to terms that obligate you
+to collect a royalty for further conveying from those to whom you convey
+the Program, the only way you could satisfy both those terms and this
+License would be to refrain entirely from conveying the Program.
+
+ 13. Use with the GNU Affero General Public License.
+
+ Notwithstanding any other provision of this License, you have
+permission to link or combine any covered work with a work licensed
+under version 3 of the GNU Affero General Public License into a single
+combined work, and to convey the resulting work. The terms of this
+License will continue to apply to the part which is the covered work,
+but the special requirements of the GNU Affero General Public License,
+section 13, concerning interaction through a network will apply to the
+combination as such.
+
+ 14. Revised Versions of this License.
+
+ The Free Software Foundation may publish revised and/or new versions of
+the GNU General Public License from time to time. Such new versions will
+be similar in spirit to the present version, but may differ in detail to
+address new problems or concerns.
+
+ Each version is given a distinguishing version number. If the
+Program specifies that a certain numbered version of the GNU General
+Public License "or any later version" applies to it, you have the
+option of following the terms and conditions either of that numbered
+version or of any later version published by the Free Software
+Foundation. If the Program does not specify a version number of the
+GNU General Public License, you may choose any version ever published
+by the Free Software Foundation.
+
+ If the Program specifies that a proxy can decide which future
+versions of the GNU General Public License can be used, that proxy's
+public statement of acceptance of a version permanently authorizes you
+to choose that version for the Program.
+
+ Later license versions may give you additional or different
+permissions. However, no additional obligations are imposed on any
+author or copyright holder as a result of your choosing to follow a
+later version.
+
+ 15. Disclaimer of Warranty.
+
+ THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
+APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
+HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
+OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
+THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
+PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
+IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
+ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
+
+ 16. Limitation of Liability.
+
+ IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
+WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
+THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
+GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
+USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
+DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
+PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
+EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
+SUCH DAMAGES.
+
+ 17. Interpretation of Sections 15 and 16.
+
+ If the disclaimer of warranty and limitation of liability provided
+above cannot be given local legal effect according to their terms,
+reviewing courts shall apply local law that most closely approximates
+an absolute waiver of all civil liability in connection with the
+Program, unless a warranty or assumption of liability accompanies a
+copy of the Program in return for a fee.
+
+ END OF TERMS AND CONDITIONS
+
+ How to Apply These Terms to Your New Programs
+
+ If you develop a new program, and you want it to be of the greatest
+possible use to the public, the best way to achieve this is to make it
+free software which everyone can redistribute and change under these terms.
+
+ To do so, attach the following notices to the program. It is safest
+to attach them to the start of each source file to most effectively
+state the exclusion of warranty; and each file should have at least
+the "copyright" line and a pointer to where the full notice is found.
+
+ <one line to give the program's name and a brief idea of what it does.>
+ Copyright (C) <year> <name of author>
+
+ This program is free software: you can redistribute it and/or modify
+ it under the terms of the GNU General Public License as published by
+ the Free Software Foundation, either version 3 of the License, or
+ (at your option) any later version.
+
+ This program is distributed in the hope that it will be useful,
+ but WITHOUT ANY WARRANTY; without even the implied warranty of
+ MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
+ GNU General Public License for more details.
+
+ You should have received a copy of the GNU General Public License
+ along with this program. If not, see <https://www.gnu.org/licenses/>.
+
+Also add information on how to contact you by electronic and paper mail.
+
+ If the program does terminal interaction, make it output a short
+notice like this when it starts in an interactive mode:
+
+ <program> Copyright (C) <year> <name of author>
+ This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
+ This is free software, and you are welcome to redistribute it
+ under certain conditions; type `show c' for details.
+
+The hypothetical commands `show w' and `show c' should show the appropriate
+parts of the General Public License. Of course, your program's commands
+might be different; for a GUI interface, you would use an "about box".
+
+ You should also get your employer (if you work as a programmer) or school,
+if any, to sign a "copyright disclaimer" for the program, if necessary.
+For more information on this, and how to apply and follow the GNU GPL, see
+<https://www.gnu.org/licenses/>.
+
+ The GNU General Public License does not permit incorporating your program
+into proprietary programs. If your program is a subroutine library, you
+may consider it more useful to permit linking proprietary applications with
+the library. If this is what you want to do, use the GNU Lesser General
+Public License instead of this License. But first, please read
+<https://www.gnu.org/licenses/why-not-lgpl.html>.
diff --git a/README.md b/README.md
new file mode 100644
index 0000000000000000000000000000000000000000..382bf31d733f2959682cf3bddeefc15c03f19a4c
--- /dev/null
+++ b/README.md
@@ -0,0 +1,52 @@
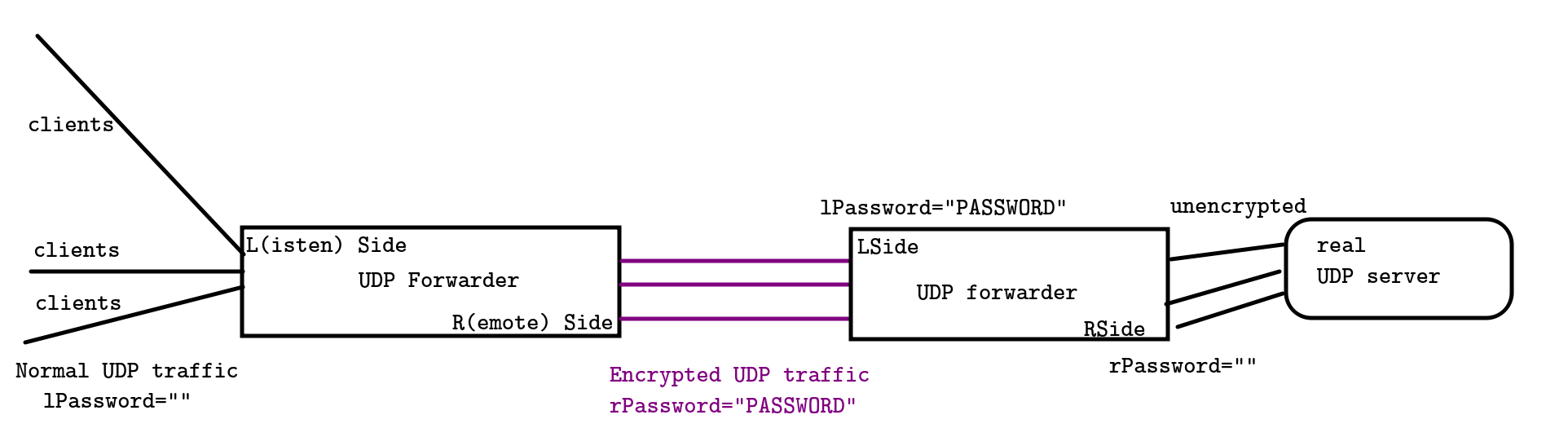
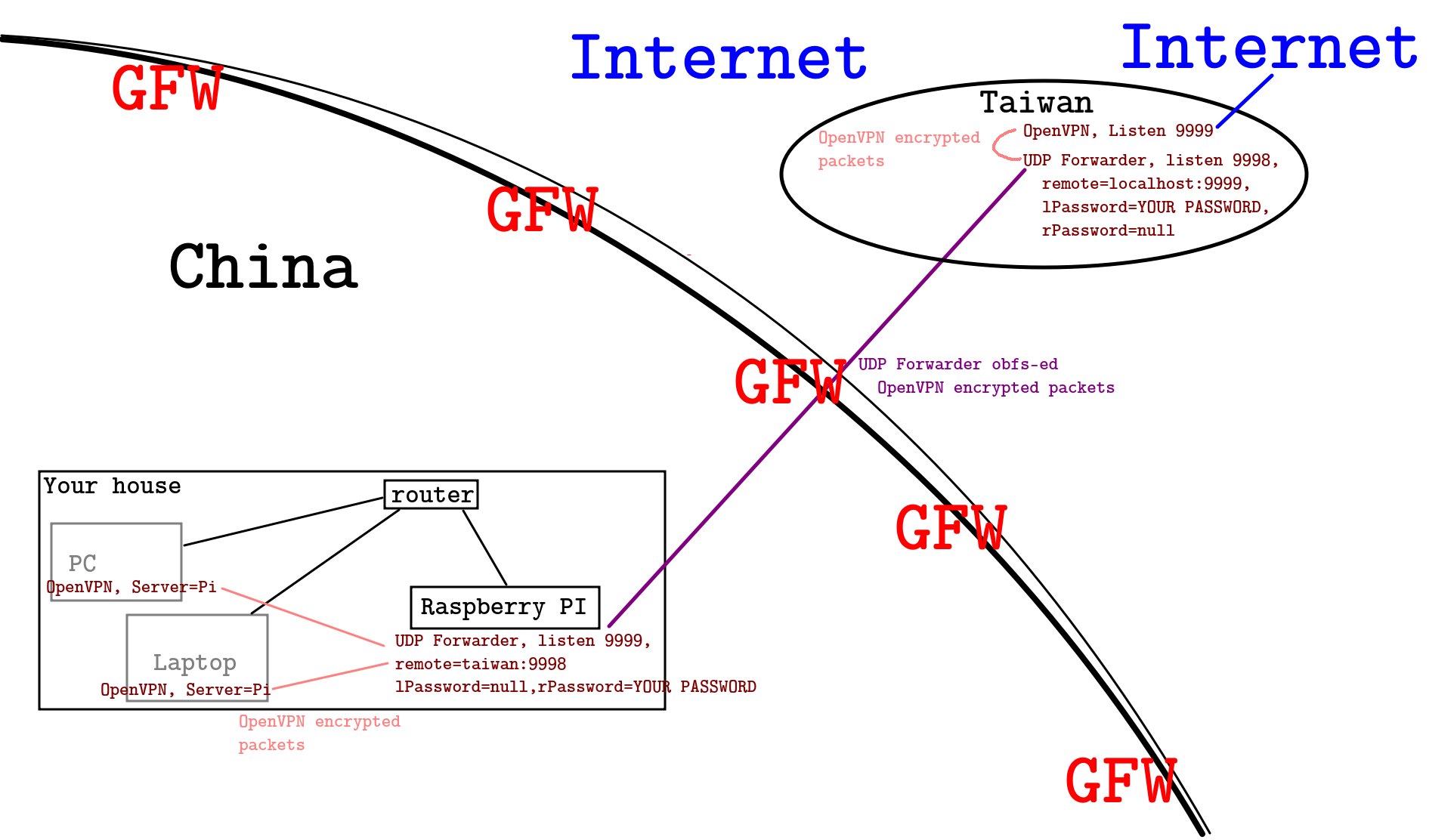
+# UDP forwarder
+
+A simple **UNSAFE** tool to encrypt / hide your UDP packets. Trying to trick The Great Firewall deep learning VPN detection
+model. The packet can be easily decrypted if attacker checks the source code.
+
+This tool is usually used with OpenVPN, to avoid being `deep-learned` by the GFW. OpenVPN already encrypted the packets,
+so I needn't do it again.
+
+## NOTE
+
+DO NOT USE MASTER BRANCH. It's still under debugging. (the connection migration is not stable)
+
+## Design
+
+
+
+## Build
+
+```
+mkdir build && cd build
+cmake .. && make
+./udp_forwarder_ng [args ...]
+```
+
+## Common Deployment
+
+
+
+## Common mistake
+
+If you run OpenVPN and udp_forwarder on the same PC, you won't access the Internet successfully.
+If you did it, please think again and you'll realize how stupid you are.
+
+## Naive performance test
+
+Note: the connection setup procedure maybe a little slow, but it doesn't matter.
+
+- Latency
+
+with proxy: (encrypted OpenVPN + encrypted&obfs udp_forwarder_ng) 70.386ms
+
+without proxy: 0.475ms + 68.578ms = 69.053ms
+
+overhead (OpenVPN+Forwarder): 1.333ms
+
+## Known bug
+
+Every UDP Forwarder, will drop the first client2server packet. (Doesn't matter).
+
+Every UDP Forwarder, will drop
+
+I assume that every connection has a unique port. search for comment tag `1632`
diff --git a/Util.hpp b/Util.hpp
new file mode 100644
index 0000000000000000000000000000000000000000..530e3381d2ffb41e0cfcabcd4e625db395d11ba0
--- /dev/null
+++ b/Util.hpp
@@ -0,0 +1,149 @@
+//
+// Created by recolic on 19-6-10.
+//
+
+#ifndef UDP_FORWARDER_NG_CONNECTIONTIMEOUTCTL_HPP
+#define UDP_FORWARDER_NG_CONNECTIONTIMEOUTCTL_HPP
+
+
+#include <cstddef>
+#include <rlib/sys/fd.hpp>
+#include <ctime>
+#include <rlib/log.hpp>
+
+extern rlib::logger rlog;
+
+inline size_t getWallTime() {
+ auto seconds = static_cast<size_t>(std::time(nullptr));
+ return seconds / SERVER_ENCRYPT_CONNECTION_TIMEOUT_SECONDS;
+}
+
+
+inline char nibbleToHex(int nibble)
+{
+ const int ascii_zero = 48;
+ const int ascii_a = 65;
+
+ if((nibble >= 0) && (nibble <= 9))
+ {
+ return (char) (nibble + ascii_zero);
+ }
+ if((nibble >= 10) && (nibble <= 15))
+ {
+ return (char) (nibble - 10 + ascii_a);
+ }
+ return '?';
+}
+inline string char2str(char byteVal)
+{
+ int upp = (byteVal & 0xF0) >> 4;
+ int low = (byteVal & 0x0F);
+ return std::string() + nibbleToHex(upp) + nibbleToHex(low);
+}
+
+template <typename T>
+inline string printBinaryObj(const T &obj) {
+ string res = "[";
+ const char *p = (const char *)&obj;
+ for(auto i = 0; i < sizeof(T); ++i) {
+ res += char2str(p[i]) + ' ';
+ }
+ return res + "]";
+}
+
+struct clientInfo {
+ sockaddr_storage addr; socklen_t len;
+ bool operator==(const clientInfo &another) const {
+ return do_compare(another, true);
+ }
+ bool matchWildcard(const clientInfo &another) const {
+ return do_compare(another, false);
+ }
+ bool do_compare(const clientInfo &another, bool need_same_addr = true) const {
+ const auto *me = (const sockaddr_in*)&this->addr;
+ const auto *an = (const sockaddr_in*)&another.addr;
+
+ if(me->sin_family != an->sin_family)
+ return false;
+ if(me->sin_family == AF_INET) {
+ auto same_addr = std::memcmp(&me->sin_addr, &an->sin_addr, sizeof(me->sin_addr)) == 0;
+ auto same_port = me->sin_port == an->sin_port;
+ return need_same_addr ? same_addr && same_port : same_port;
+ }
+ else if(me->sin_family == AF_INET6) {
+ const auto *me = (const sockaddr_in6*)&this->addr;
+ const auto *an = (const sockaddr_in6*)&another.addr;
+ auto same_addr = std::memcmp(&me->sin6_addr, &an->sin6_addr, sizeof(me->sin6_addr)) == 0;
+ auto same_port = me->sin6_port == an->sin6_port;
+ return need_same_addr ? same_addr && same_port : same_port;
+ }
+ else
+ throw std::runtime_error("Invalid client info: sin_family is not AF_INET or AF_INET6");
+ }
+ bool isNull() const {
+ for(auto cter = 0; cter < sizeof(addr); ++cter) {
+ if(cter[(char *)&addr] != 0)
+ return false;
+ }
+ return true;
+ }
+ uint16_t getPortNum() const {
+ const auto *me = (const sockaddr_in*)&this->addr;
+ if(me->sin_family == AF_INET) {
+ return me->sin_port;
+
+ }
+ else if(me->sin_family == AF_INET6) {
+ const auto *me = (const sockaddr_in6*)&this->addr;
+ return me->sin6_port;
+ }
+ else
+ throw std::runtime_error("Invalid client info: sin_family is not AF_INET or AF_INET6: got " + std::to_string(me->sin_family));
+ }
+ void setPortNum(uint16_t port) {
+ auto *me = (sockaddr_in*)&this->addr;
+ if(me->sin_family == AF_INET) {
+ me->sin_port = port;
+ }
+ else if(me->sin_family == AF_INET6) {
+ auto *me = (sockaddr_in6*)&this->addr;
+ me->sin6_port = port;
+ }
+ else
+ throw std::runtime_error("Invalid client info: sin_family is not AF_INET or AF_INET6: got " + std::to_string(me->sin_family));
+ }
+};
+struct clientInfoHash {std::size_t operator()(const clientInfo &info) const {return *(std::size_t*)&info.addr;}}; // hash basing on port number and part of ip (v4/v6) address.
+
+//// Change connection to encrypted server in every 1 minute to avoid GFW deep-packet-inspect.
+//class ConnectionTimeoutCtl {
+//public:
+// ConnectionTimeoutCtl(size_t timeoutSeconds, bool serverSideIsEncrypted)
+// : timeoutSeconds(timeoutSeconds), serverSideIsEncrypted(serverSideIsEncrypted) {
+// // If server side is unencrypted, set timeout to +inf.
+// }
+//
+// bool encryptedMessageIsControlMessage() {
+// // Client side operation.
+// // 1. Return true if the message is control message (nonce=0)
+// // 2. if the message is control msg, deal with it.
+// }
+//
+// fd_t shouldChangeConnection() {
+// // Server side operation.
+// // 1. Return new fd ONLY if the connection should time out AND the new connection is ready.
+// // else return -1.
+// // 2. This function should send the control message, and update the client2server map.
+// }
+//
+//
+
+
+
+//private:
+// size_t timeoutSeconds;
+// bool serverSideIsEncrypted;
+//};
+
+
+#endif //UDP_FORWARDER_NG_CONNECTIONTIMEOUTCTL_HPP
diff --git a/main.cc b/main.cc
index bbe4c75e97b234f100a8f37cecce6fe324d0b03c..3043fe8b0a3e5600fe589770835a036481a7bc30 100644
--- a/main.cc
+++ b/main.cc
@@ -1,19 +1,41 @@
#include <iostream>
#include <rlib/stdio.hpp>
#include <rlib/opt.hpp>
+#include "Forwarder.hpp"
+
+rlib::logger rlog(std::cerr);
+
using namespace rlib::literals;
int main(int argc, char **argv) {
rlib::opt_parser args(argc, argv);
if(args.getBoolArg("--help", "-h")) {
- rlib::println("Usage: {} -l listenAddr -p listenPort -s serverAddr -P serverPort -lp LPassword -rp R(emote)Password"_rs.format(args.getSelf()));
+ rlib::println("Usage: {} -l listenAddr -p listenPort -s serverAddr -P serverPort [-lp LPassword] [-rp R(emote)Password] [--log=error/info/verbose/debug]"_rs.format(args.getSelf()));
+ rlib::println("Leave LPassword for empty if listenAddr is other UDP application.");
+ rlib::println("Leave RPassword for empty if serverAddr is other UDP application.");
+ return 0;
}
auto listenAddr = args.getValueArg("-l");
auto listenPort = args.getValueArg("-p").as<uint16_t>();
auto serverAddr = args.getValueArg("-s");
auto serverPort = args.getValueArg("-P").as<uint16_t>();
- auto lPassword = args.getValueArg("-lp");
- auto rPassword = args.getValueArg("-rp");
+ auto lPassword = args.getValueArg("-lp", false, "");
+ auto rPassword = args.getValueArg("-rp", false, "");
+
+ auto log_level = args.getValueArg("--log", false, "info");
+ if(log_level == "error")
+ rlog.set_log_level(rlib::log_level_t::ERROR);
+ else if(log_level == "info")
+ rlog.set_log_level(rlib::log_level_t::INFO);
+ else if(log_level == "verbose")
+ rlog.set_log_level(rlib::log_level_t::VERBOSE);
+ else if(log_level == "debug")
+ rlog.set_log_level(rlib::log_level_t::DEBUG);
+ else
+ throw std::runtime_error("Unknown log level: " + log_level);
+
+ Forwarder fwd(listenAddr, listenPort, serverAddr, serverPort, lPassword, rPassword);
+ fwd.run();
return 0;
}
\ No newline at end of file
diff --git a/res/explain.png b/res/explain.png
new file mode 100644
index 0000000000000000000000000000000000000000..e00cb126ff77bbe8f0203e7494f041f574d3633b
Binary files /dev/null and b/res/explain.png differ
diff --git a/res/solu.png b/res/solu.png
new file mode 100644
index 0000000000000000000000000000000000000000..b251750fc65fd36faebf40da7bd12e260c4846ed
Binary files /dev/null and b/res/solu.png differ